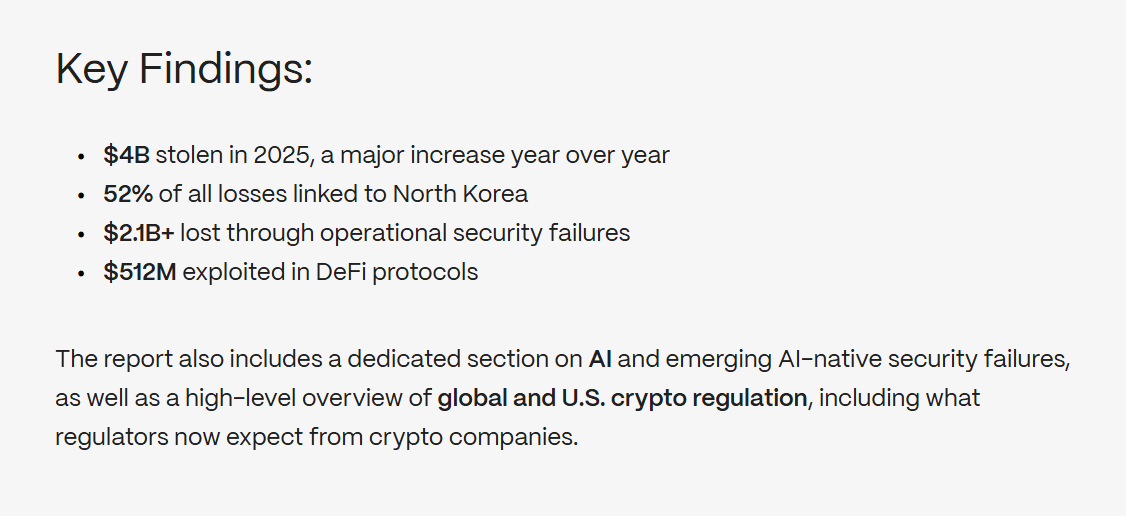
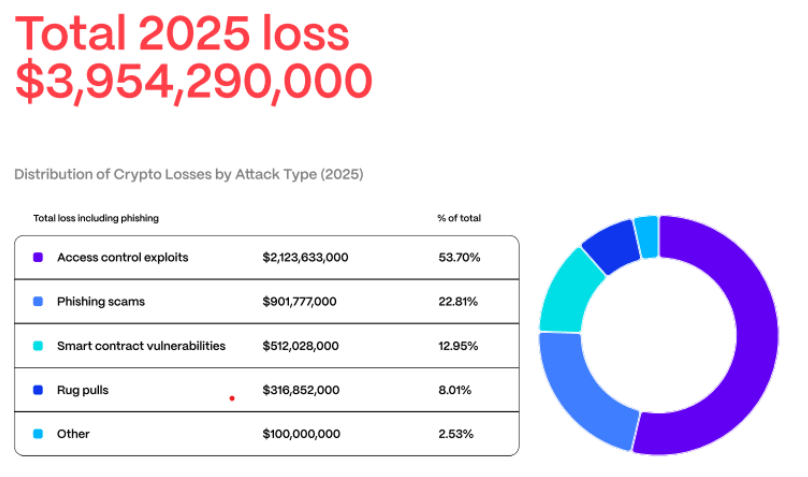
Hacken’s 2025 yearly security report also found that total Web3 losses rose to about $3.95 billion, up roughly $1.1 billion from 2024, with more than half of the losses linked to North Korean threat actors. The report shows that most losses were caused by access control failures and operational security weaknesses, like compromised keys and poor off-boarding practices, rather than smart contract bugs.
ZachXBT Traces Coinbase Impersonation Scam
A scammer posing as a Coinbase help desk worker
The investigator alleged that the suspect, described as a “Canadian threat actor,” carried out Coinbase support impersonation scams over the past year by using social engineering
X post from ZachXBT
While specific technical details of each incident were not shared, the scams reportedly relied on classic social engineering techniques, where attackers pose as trusted figures to gain victims’ confidence and extract sensitive information or convince them to make fraudulent transactions.
ZachXBT said the suspect tried to cover his tracks by repeatedly purchasing expensive Telegram
ZachXBT also claimed to have identified the alleged scammer’s home address by using publicly available information, though he said he would not publish it due to platform rules. Screenshots shared alongside the post showed what he described as repeated lapses in operational security, including selfies and stories flaunting a lavish lifestyle.
Social engineering attacks in crypto is a big issue. Best practices include never responding to unsolicited calls or messages claiming to be from an exchange
Web3 Losses Hit $3.95B in 2025
Web3
Data shows that losses were heavily front-loaded, peaking at over $2 billion in the first quarter of the year before falling steadily to around $350 million by the fourth quarter. While the decline later in the year may suggest progress, Hacken warned that the overall pattern points to deep, systemic operational weaknesses rather than a temporary spike caused by isolated software bugs.
Key findings from Hacken’s 2025 security report
According to the report, 2025 made one trend unmistakably clear: while smart contract vulnerabilities
Weak key management, compromised signers, and poor off-boarding practices were identified as the dominant causes of major incidents. Hacken estimates that access control and related operational failures accounted for approximately $2.12 billion, or almost 54% of all losses during the year, compared with about $512 million tied to smart contract
Crypto losses by attack type (Source: Hacken)
A single incident played a huge role in shaping the year’s statistics. The breach at Bybit
Hacken’s forensic team pointed out that regulators across major jurisdictions, including the United States and the European Union, have laid out what robust operational security
Despite this, Hacken said many Web3 companies continued to operate with insecure practices throughout 2025. Yehor Rudystia, head of forensic at Hacken Extractor, pointed to recurring issues like failing to revoke developer access during off-boarding, relying on a single private key to manage critical protocol functions, and not deploying Endpoint Detection and Response systems. He explained that measures like regular penetration testing, incident response simulations, custody control reviews, and independent audits should be considered non-negotiable for large exchanges and custodians going into 2026.
Looking ahead, Hacken expects regulatory oversight to shift from soft guidance toward enforceable requirements. Co-founder and CEO Yevheniia Broshevan said the industry has a clear opportunity to raise its security baseline by adopting dedicated signing hardware and essential monitoring tools as standard practice.